Организация VPN-сети (часть шестая)
Теперь нам нужно обеспечить шифрование передаваемых данных и организовать контроль доступа к нашим ресурсам. Для этого разворачиваем собственную VPN-инфраструктуру поверх каналов Казахтелекома. Существует несколько реализаций технологии VPN, в нашем случае подойдет пакет OpenVPN, в котором реализован весь нужный нам функционал.
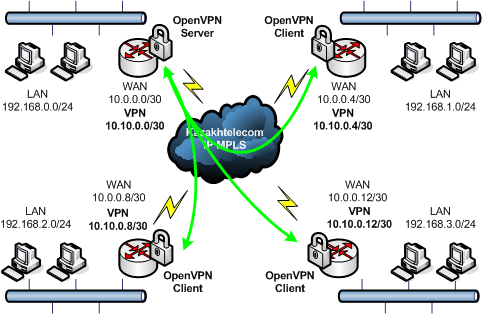
Структура подобной сети достаточно простая – один из узлов сети объявляется VPN-сервером; другие узлы, выступающие VPN-клиентами, могут подключаться к сети после аутентификации на VPN-сервере, при этом данные между клиентами и сервером передаются в зашифрованном виде. Результатом наших действий будет виртуальная сеть, построенная по такой схеме:
Устанавливаем VPN-сервер
В качестве VPN-сервера настраиваем один из маршрутизаторов нашей сети (используйте маршрутизатор головного филиала или того филиала, который географически находится ближе к вам). Сначала проверьте, присутствует ли пакет openvpn в репозиториях вашего дистрибутива:
[root@gateway1 ~]# yum search openvpn lzo Loading "fastestmirror" plugin Loading mirror speeds from cached hostfile * base: mirror.corbina.net * updates: mirror.corbina.net * addons: mirror.corbina.net * extras: centosr3.centos.org openvpn.i386 : OpenVPN is a robust and highly flexible VPN daemon by James Yonan. lzo-devel.i386 : Header files, libraries and development documentation for lzo lzo.i386 : Portable lossless data compression library [root@gateway1 ~]#
Если пакеты найдены, устанавливаем:
[root@gateway1 ~]# yum install openvpn lzo
в ином случае, готовые пакеты для RHEL5/CentOS можно скачать отсюда.
После установки конфигурируем службу в режиме сервера. Копируем пример конфигурационного файла /usr/share/doc/openvpn-2.0.9/sample-config-files/server.conf в каталог /etc/openvpn и редактируем в соответствии с нашими условиями.
Файл /etc/openvpn/server.conf:
############################################################ # OpenVPN 2.0 config file for multi-client server. # ############################################################ # Which local IP address should OpenVPN # listen on? (optional) ;local a.b.c.d # Which TCP/UDP port should OpenVPN listen on? # If you want to run multiple OpenVPN instances # on the same machine, use a different port # number for each one. You will need to # open up this port on your firewall. port 1194 # TCP or UDP server? ;proto tcp proto udp # "dev tun" will create a routed IP tunnel, # "dev tap" will create an ethernet tunnel. # Use "dev tap0" if you are ethernet bridging # and have precreated a tap0 virtual interface # and bridged it with your ethernet interface. # If you want to control access policies # over the VPN, you must create firewall # rules for the the TUN/TAP interface. # On non-Windows systems, you can give # an explicit unit number, such as tun0. # On Windows, use "dev-node" for this. # On most systems, the VPN will not function # unless you partially or fully disable # the firewall for the TUN/TAP interface. ;dev tap dev tun0 # Windows needs the TAP-Win32 adapter name # from the Network Connections panel if you # have more than one. On XP SP2 or higher, # you may need to selectively disable the # Windows firewall for the TAP adapter. # Non-Windows systems usually don't need this. ;dev-node MyTap # SSL/TLS root certificate (ca), certificate # (cert), and private key (key). Each client # and the server must have their own cert and # key file. The server and all clients will # use the same ca file. # # See the "easy-rsa" directory for a series # of scripts for generating RSA certificates # and private keys. Remember to use # a unique Common Name for the server # and each of the client certificates. # # Any X509 key management system can be used. # OpenVPN can also use a PKCS #12 formatted key file # (see "pkcs12" directive in man page). ca ca.crt cert server.crt key server.key # This file should be kept secret # Diffie hellman parameters. # Generate your own with: # openssl dhparam -out dh1024.pem 1024 # Substitute 2048 for 1024 if you are using # 2048 bit keys. dh dh1024.pem # Configure server mode and supply a VPN subnet # for OpenVPN to draw client addresses from. # The server will take 10.8.0.1 for itself, # the rest will be made available to clients. # Each client will be able to reach the server # on 10.8.0.1. Comment this line out if you are # ethernet bridging. See the man page for more info. server 10.10.0.0 255.255.255.0 # -- server --: # 10.10.0.0/30 (main-filial) # host 10.10.0.1, gw 10.10.0.2, bcast 10.10.0.2 # -- clients --: # 10.10.0.4/30 (filial2) # host 10.10.0.5, gw 10.10.0.6, bcast 10.10.0.7 # 10.10.0.8/30 (filial3) # host 10.10.0.9, gw 10.10.0.10, bcast 10.10.0.11 # 10.10.0.12/30 (filial4) # host 10.10.0.13, gw 10.10.0.14, bcast 10.10.0.15 # .. etc.. # Maintain a record of client <-> virtual IP address # associations in this file. If OpenVPN goes down or # is restarted, reconnecting clients can be assigned # the same virtual IP address from the pool that was # previously assigned. ifconfig-pool-persist ipp.txt # Configure server mode for ethernet bridging. # You must first use your OS's bridging capability # to bridge the TAP interface with the ethernet # NIC interface. Then you must manually set the # IP/netmask on the bridge interface, here we # assume 10.8.0.4/255.255.255.0. Finally we # must set aside an IP range in this subnet # (start=10.8.0.50 end=10.8.0.100) to allocate # to connecting clients. Leave this line commented # out unless you are ethernet bridging. ;server-bridge 10.8.0.4 255.255.255.0 10.8.0.50 10.8.0.100 # Push routes to the client to allow it # to reach other private subnets behind # the server. Remember that these # private subnets will also need # to know to route the OpenVPN client # address pool (10.8.0.0/255.255.255.0) # back to the OpenVPN server. ;push "route 192.168.10.0 255.255.255.0" ;push "route 192.168.20.0 255.255.255.0" # To assign specific IP addresses to specific # clients or if a connecting client has a private # subnet behind it that should also have VPN access, # use the subdirectory "ccd" for client-specific # configuration files (see man page for more info). # EXAMPLE: Suppose the client # having the certificate common name "Thelonious" # also has a small subnet behind his connecting # machine, such as 192.168.40.128/255.255.255.248. # First, uncomment out these lines: client-config-dir ccd ;route 192.168.40.128 255.255.255.248 # Then create a file ccd/Thelonious with this line: # iroute 192.168.40.128 255.255.255.248 # This will allow Thelonious' private subnet to # access the VPN. This example will only work # if you are routing, not bridging, i.e. you are # using "dev tun" and "server" directives. # EXAMPLE: Suppose you want to give # Thelonious a fixed VPN IP address of 10.9.0.1. # First uncomment out these lines: ;client-config-dir ccd ;route 10.9.0.0 255.255.255.252 # Then add this line to ccd/Thelonious: # ifconfig-push 10.9.0.1 10.9.0.2 # Suppose that you want to enable different # firewall access policies for different groups # of clients. There are two methods: # (1) Run multiple OpenVPN daemons, one for each # group, and firewall the TUN/TAP interface # for each group/daemon appropriately. # (2) (Advanced) Create a script to dynamically # modify the firewall in response to access # from different clients. See man # page for more info on learn-address script. ;learn-address ./script # If enabled, this directive will configure # all clients to redirect their default # network gateway through the VPN, causing # all IP traffic such as web browsing and # and DNS lookups to go through the VPN # (The OpenVPN server machine may need to NAT # the TUN/TAP interface to the internet in # order for this to work properly). # CAVEAT: May break client's network config if # client's local DHCP server packets get routed # through the tunnel. Solution: make sure # client's local DHCP server is reachable via # a more specific route than the default route # of 0.0.0.0/0.0.0.0. ;push "redirect-gateway local def1" push "redirect-gateway def1" # Certain Windows-specific network settings # can be pushed to clients, such as DNS # or WINS server addresses. CAVEAT: # http://openvpn.net/faq.html#dhcpcaveats ;push "dhcp-option DNS 10.8.0.1" ;push "dhcp-option WINS 10.8.0.1" # Uncomment this directive to allow different # clients to be able to "see" each other. # By default, clients will only see the server. # To force clients to only see the server, you # will also need to appropriately firewall the # server's TUN/TAP interface. ;client-to-client # Uncomment this directive if multiple clients # might connect with the same certificate/key # files or common names. This is recommended # only for testing purposes. For production use, # each client should have its own certificate/key # pair. # # IF YOU HAVE NOT GENERATED INDIVIDUAL # CERTIFICATE/KEY PAIRS FOR EACH CLIENT, # EACH HAVING ITS OWN UNIQUE "COMMON NAME", # UNCOMMENT THIS LINE OUT. ;duplicate-cn # The keepalive directive causes ping-like # messages to be sent back and forth over # the link so that each side knows when # the other side has gone down. # Ping every 10 seconds, assume that remote # peer is down if no ping received during # a 120 second time period. keepalive 10 120 # For extra security beyond that provided # by SSL/TLS, create an "HMAC firewall" # to help block DoS attacks and UDP port flooding. # # Generate with: # openvpn --genkey --secret ta.key # # The server and each client must have # a copy of this key. # The second parameter should be '0' # on the server and '1' on the clients. ;tls-auth ta.key 0 # This file is secret # Select a cryptographic cipher. # This config item must be copied to # the client config file as well. ;cipher BF-CBC # Blowfish (default) ;cipher AES-128-CBC # AES ;cipher DES-EDE3-CBC # Triple-DES # Enable compression on the VPN link. # If you enable it here, you must also # enable it in the client config file. comp-lzo # The maximum number of concurrently connected # clients we want to allow. ;max-clients 100 # It's a good idea to reduce the OpenVPN # daemon's privileges after initialization. # # You can uncomment this out on # non-Windows systems. user nobody group nobody # The persist options will try to avoid # accessing certain resources on restart # that may no longer be accessible because # of the privilege downgrade. persist-key persist-tun # Output a short status file showing # current connections, truncated # and rewritten every minute. status /var/log/openvpn-status.log # By default, log messages will go to the syslog (or # on Windows, if running as a service, they will go to # the "\Program Files\OpenVPN\log" directory). # Use log or log-append to override this default. # "log" will truncate the log file on OpenVPN startup, # while "log-append" will append to it. Use one # or the other (but not both). ;log openvpn.log log-append /var/log/openvpn.log # Set the appropriate level of log # file verbosity. # # 0 is silent, except for fatal errors # 4 is reasonable for general usage # 5 and 6 can help to debug connection problems # 9 is extremely verbose verb 3 # Silence repeating messages. At most 20 # sequential messages of the same message # category will be output to the log. ;mute 20
Создаем PKI-инфраструктуру на сервере. Копируем каталог /usr/share/doc/openvpn-2.0.9/easy-rsa в /etc/openvpn, редактируем файл настроек vars.
Файл /etc/openvpn/easy-rsa/vars:
-------- < начало пропущено > -------- # These are the default values for fields # which will be placed in the certificate. # Don't leave any of these fields blank. export KEY_COUNTRY=KZ export KEY_PROVINCE=Kostanay export KEY_CITY=Kostanay export KEY_ORG="YourCompany LLC" export KEY_EMAIL="denis@fateyev.com"
Активизируем изменения (обратите внимание на пробел в '. ./vars'):
[root@gateway1 easy-rsa]# . ./vars [root@gateway1 easy-rsa]# ./clean-all
Создаем корневой сертификат:
[root@gateway1 easy-rsa]# ./build-ca Generating a 1024 bit RSA private key ………………………++++++ …………………….++++++ writing new private key to ‘ca.key’ —– You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter ‘.’, the field will be left blank. —– Country Name (2 letter code) [KZ]: State or Province Name (full name) [Kostanay]: Locality Name (eg, city) [Kostanay]: Organization Name (eg, company) [YourCompany LLC]: Organizational Unit Name (eg, section) []:Tech Staff Common Name (eg, your name or your server’s hostname) []:vpn.yourcompany.com Email Address [denis@fateyev.com]:
Создаем сертификат сервера:
[root@gateway1 easy-rsa]# ./build-key-server server Generating a 1024 bit RSA private key ………………………………….++++++ …………………….++++++ writing new private key to ‘server.key’ —– You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter ‘.’, the field will be left blank. —– Country Name (2 letter code) [KZ]: State or Province Name (full name) [Kostanay]: Locality Name (eg, city) [Kostanay]: Organization Name (eg, company) [YourCompany LLC]: Organizational Unit Name (eg, section) []:Tech Staff Common Name (eg, your name or your server’s hostname) []:vpn.yourcompany.com Email Address [denis@fateyev.com]: Please enter the following ‘extra’ attributes to be sent with your certificate request A challenge password []:<enter your password here> An optional company name []: Using configuration from /etc/openvpn/easy-rsa/openssl.cnf Check that the request matches the signature Signature ok The Subject’s Distinguished Name is as follows countryName :PRINTABLE:’KZ’ stateOrProvinceName :PRINTABLE:’Kostanay’ localityName :PRINTABLE:’Kostanay’ organizationName :PRINTABLE:’YourCompany LLC’ organizationalUnitName:PRINTABLE:’Tech Staff’ commonName :PRINTABLE:’vpn.yourcompany.com’ emailAddress :IA5STRING:’denis@fateyev.com’ Certificate is to be certified until Jun 02 11:52:31 2019 GMT (3650 days) Sign the certificate? [y/n]:y 1 out of 1 certificate requests certified, commit? [y/n]y Write out database with 1 new entries Data Base Updated
С помощью алгоритма Diffie-Hellman генерируем секретный ключ:
[root@gateway1 easy-rsa]# ./build-dh Generating DH parameters, 1024 bit long safe prime, generator 2 This is going to take a long time
Копируем файлы ca.crt, dh1024.pem, server.key, server.crt из папки keys/ в /etc/openvpn:
[root@gateway1 easy-rsa]# cp keys/ca.crt keys/dh1024.pem \ keys/server.key keys/server.crt /etc/openvpn/
Разрешаем подключения к OpenVPN-серверу (добавляем запись в конфигурационный файл /etc/sysconfig/iptables в секцию *filter):
-A INPUT -m state --state NEW -p udp --dport 1194 -j ACCEPT
Перезапускаем iptables:
[root@gateway1 ~]# /etc/init.d/iptables restart
Создаем log-файлы для OpenVPN и назначаем права доступа:
[root@gateway1 ~]# touch /var/log/openvpn.log && \ chown nobody:nobody /var/log/openvpn.log [root@gateway1 ~]# touch /var/log/openvpn-status.log && \ chown nobody:nobody /var/log/openvpn-status.log
Служба openvpn должна запускаться при загрузке системы. Устанавливаем уровень запуска и перезапускаем службы:
[root@gateway1 ~]# chkconfig openvpn on [root@gateway1 ~]# /etc/init.d/network restart [root@gateway1 ~]# /etc/init.d/openvpn restart
Если при перезапуске openvpn присутствуют ошибки, проверьте log-файлы OpenVPN для получения дополнительной информации о неполадке. На этом настройка серверной части OpenVPN завершена.



Обсуждение